Chinese Hackers Exploit SAP NetWeaver RCE Flaw
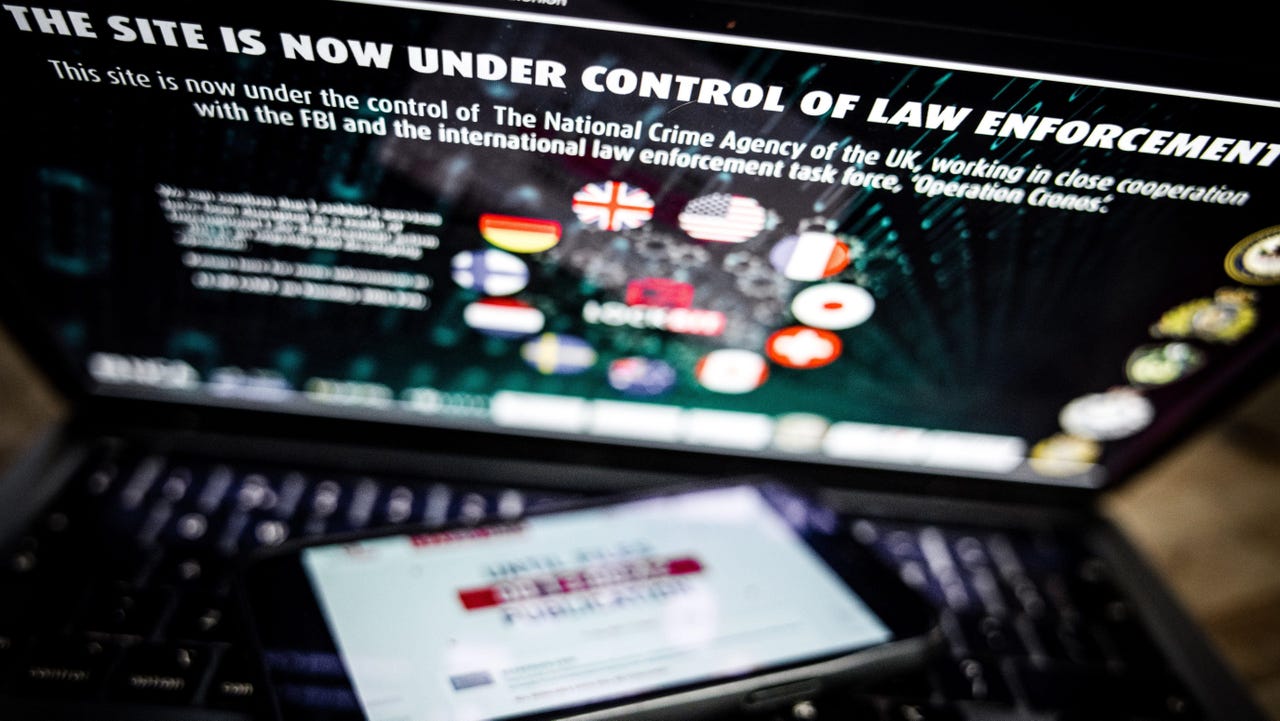
"A China-linked unnamed threat actor dubbed Chaya_004 has been observed exploiting a recently disclosed security flaw in SAP NetWeaver," reports The Hacker News: Forescout Vedere Labs, in a report published Thursday, said it uncovered a malicious infrastructure likely associated with the hacking group weaponizing CVE-2025-31324 (CVSS score: 10.0) since April 29, 2025. CVE-2025-31324 refers to a critical SAP NetWeaver flaw that allows attackers to achieve remote code execution (RCE) by uploading web shells through a susceptible "/developmentserver/metadatauploader" endpoint. The vulnerability was first flagged by ReliaQuest late last month when it found the shortcoming being abused in real-world attacks by unknown threat actors to drop web shells and the Brute Ratel C4 post-exploitation framework. According to [SAP cybersecurity firm] Onapsis, hundreds of SAP systems globally have fallen victim to attacks spanning industries and geographies, including energy and utilities, manufacturing, media and entertainment, oil and gas, pharmaceuticals, retail, and government organizations. Onapsis said it observed reconnaissance activity that involved "testing with specific payloads against this vulnerability" against its honeypots as far back as January 20, 2025. Successful compromises in deploying web shells were observed between March 14 and March 31. "In recent days, multiple threat actors are said to have jumped aboard the exploitation bandwagon to opportunistically target vulnerable systems to deploy web shells and even mine cryptocurrency..." Thanks to Slashdot reader bleedingobvious for sharing the news. Read more of this story at Slashdot.

Read more of this story at Slashdot.































































![Apple Shares 'Last Scene' Short Film Shot on iPhone 16 Pro [Video]](https://www.iclarified.com/images/news/97289/97289/97289-640.jpg)
![Apple M4 MacBook Air Hits New All-Time Low of $824 [Deal]](https://www.iclarified.com/images/news/97288/97288/97288-640.jpg)
![An Apple Product Renaissance Is on the Way [Gurman]](https://www.iclarified.com/images/news/97286/97286/97286-640.jpg)
![Apple to Sync Captive Wi-Fi Logins Across iPhone, iPad, and Mac [Report]](https://www.iclarified.com/images/news/97284/97284/97284-640.jpg)


![So your [expletive] test failed. So [obscene participle] what?](https://regmedia.co.uk/2016/08/18/shutterstock_mobile_surprise.jpg)








![What Google Messages features are rolling out [May 2025]](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2023/12/google-messages-name-cover.png?resize=1200%2C628&quality=82&strip=all&ssl=1)
![[Fixed] Gemini 2.5 Flash missing file upload for free app users](https://i0.wp.com/9to5google.com/wp-content/uploads/sites/4/2025/03/google-gemini-workspace-1.jpg?resize=1200%2C628&quality=82&strip=all&ssl=1)

















































































































































































































































































































![Ditching a Microsoft Job to Enter Startup Purgatory with Lonewolf Engineer Sam Crombie [Podcast #171]](https://cdn.hashnode.com/res/hashnode/image/upload/v1746753508177/0cd57f66-fdb0-4972-b285-1443a7db39fc.png?#)





![[DEALS] Internxt Cloud Storage Lifetime Subscription: 10TB Plan (88% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)













.png?width=1920&height=1920&fit=bounds&quality=70&format=jpg&auto=webp#)