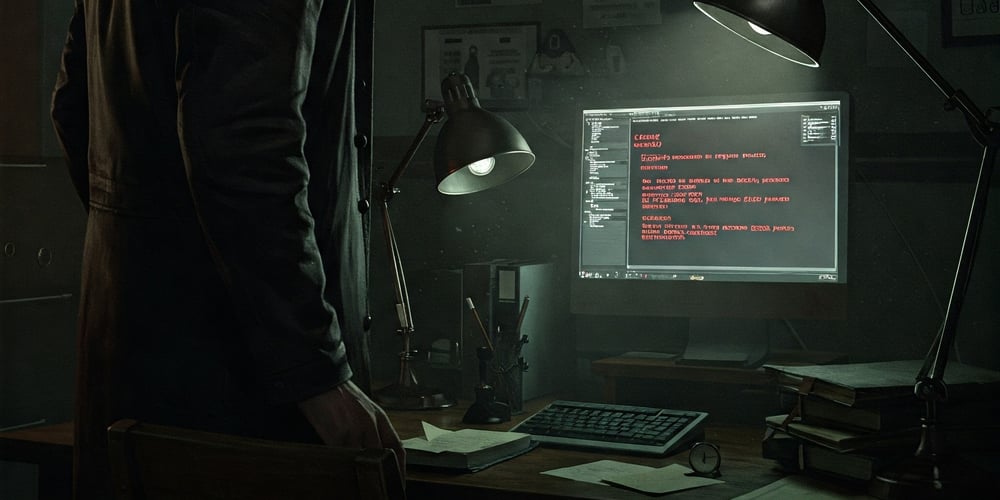
New Steganographic Malware Exploits JPEG Files to Distribute Infostealers
A sophisticated malware campaign employing steganographic techniques has recently been identified, targeting users through seemingly innocent JPEG image files. The attack leverages hidden malicious code embedded within image files that, when executed, initiates a complex chain of events designed to steal sensitive information from victims’ systems. This new threat represents a concerning evolution in malware […] The post New Steganographic Malware Exploits JPEG Files to Distribute Infostealers appeared first on Cyber Security News.

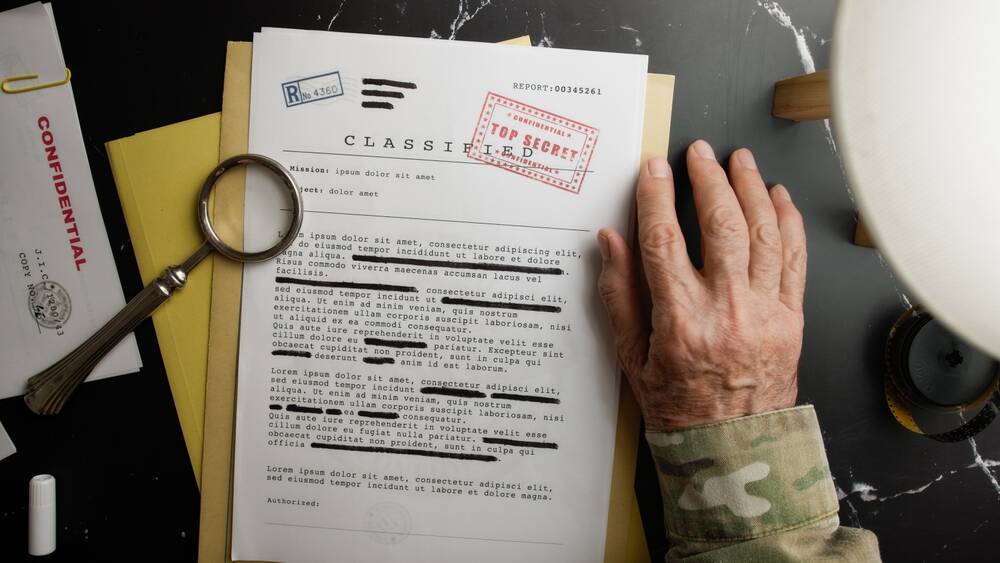
A sophisticated malware campaign employing steganographic techniques has recently been identified, targeting users through seemingly innocent JPEG image files.
The attack leverages hidden malicious code embedded within image files that, when executed, initiates a complex chain of events designed to steal sensitive information from victims’ systems.
This new threat represents a concerning evolution in malware distribution methods, combining social engineering with advanced obfuscation techniques.
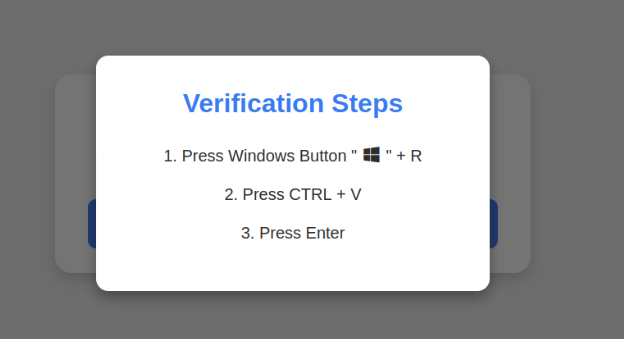
The attack begins with victims being lured into downloading what appears to be a standard JPEG file.
However, these images contain concealed malicious scripts that remain undetectable to conventional security measures.
Once the compromised file is accessed, the embedded code activates silently in the background.
Broadcom analysts detected that the malware employs a multi-stage infection process that begins with the extraction of the hidden payload from the image file.
“The steganographic technique used in this campaign is particularly sophisticated, making detection challenging for traditional security tools,” noted the researchers in their technical analysis.
Upon execution, the malware targets credential repositories in browsers, email clients, and FTP applications.
The extracted data is then exfiltrated to command-and-control servers while additional payloads are downloaded, including customized versions of known infostealer families such as Vidar, Raccoon, and Redline.
Attack Analysis
The malware authors utilized advanced obfuscation techniques, including base64 encoding within PowerShell scripts to evade detection.
The initial script, after being extracted from the JPEG file, uses Windows Script Host to execute commands with minimal visibility.
The malicious code identified includes instructions for harvesting credentials from multiple browsers, with specific functions targeting cookie files, saved passwords, and form data.
Protection against this threat is available through several security products, with specific detection signatures including ACM.Ps-Base64!g1, ISB.Downloader!gen80, and Heur.AdvML.B.
Users are advised to exercise caution when downloading image files from untrusted sources and ensure their security solutions are updated with the latest definitions.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try for Free
The post New Steganographic Malware Exploits JPEG Files to Distribute Infostealers appeared first on Cyber Security News.


















































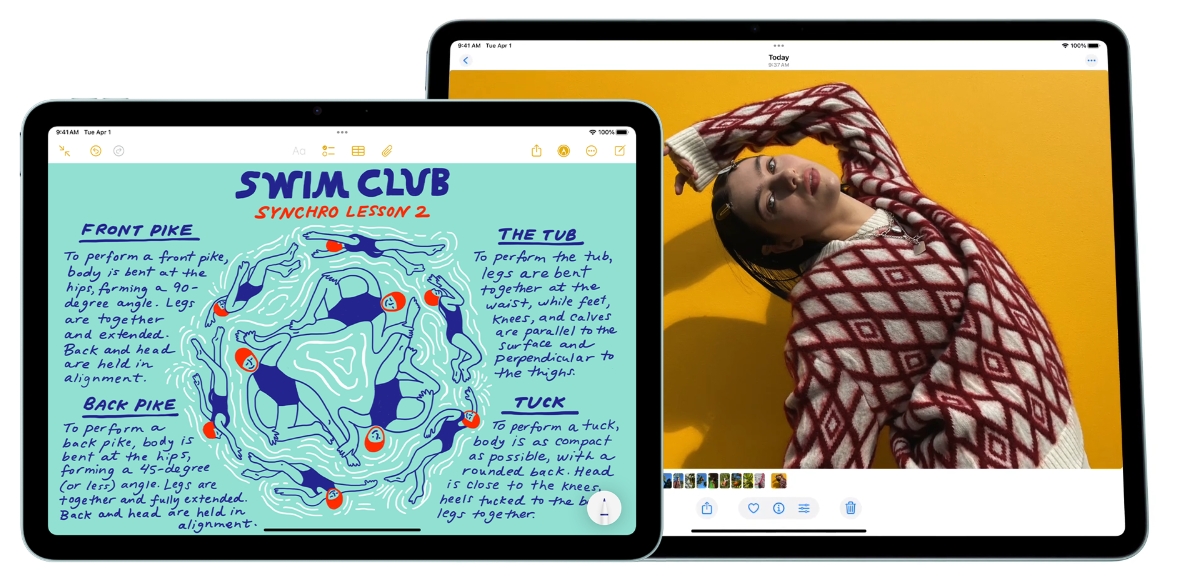









![Apple Reorganizes Executive Team to Rescue Siri [Report]](https://www.iclarified.com/images/news/96777/96777/96777-640.jpg)


















































































































































![[The AI Show Episode 139]: The Government Knows AGI Is Coming, Superintelligence Strategy, OpenAI’s $20,000 Per Month Agents & Top 100 Gen AI Apps](https://www.marketingaiinstitute.com/hubfs/ep%20139%20cover-2.png)
![[The AI Show Episode 138]: Introducing GPT-4.5, Claude 3.7 Sonnet, Alexa+, Deep Research Now in ChatGPT Plus & How AI Is Disrupting Writing](https://www.marketingaiinstitute.com/hubfs/ep%20138%20cover.png)













































































![What are good examples of 'preflight check patterns' on existing applications? [closed]](https://i.sstatic.net/yl2Tr80w.png)


















































![Release: Rendering Ranger: R² [Rewind]](https://images-3.gog-statics.com/48a9164e1467b7da3bb4ce148b93c2f92cac99bdaa9f96b00268427e797fc455.jpg)