Hackers Leveraging Fast Flux Technique to Evade Detection & Hide Malicious Servers
CISA warns of threat actors’ increasing adoption of the fast flux technique to evade detection and conceal malicious server infrastructures. As cybercriminal operations grow increasingly sophisticated, threat actors adopt advanced techniques like fast flux to mask malicious infrastructure, evade defensive measures, and maintain persistent access to compromised networks. This method, which involves rapidly cycling through domain registrations […] The post Hackers Leveraging Fast Flux Technique to Evade Detection & Hide Malicious Servers appeared first on Cyber Security News.

CISA warns of threat actors’ increasing adoption of the fast flux technique to evade detection and conceal malicious server infrastructures.
As cybercriminal operations grow increasingly sophisticated, threat actors adopt advanced techniques like fast flux to mask malicious infrastructure, evade defensive measures, and maintain persistent access to compromised networks.
This method, which involves rapidly cycling through domain registrations and hosting servers, has become a cornerstone of modern cyberattacks, from ransomware campaigns to state-sponsored espionage.
What is Fast Flux?
Fast flux is a domain-based obfuscation tactic where DNS records associated with a domain name (e.g., IP addresses) change rapidly and frequently.
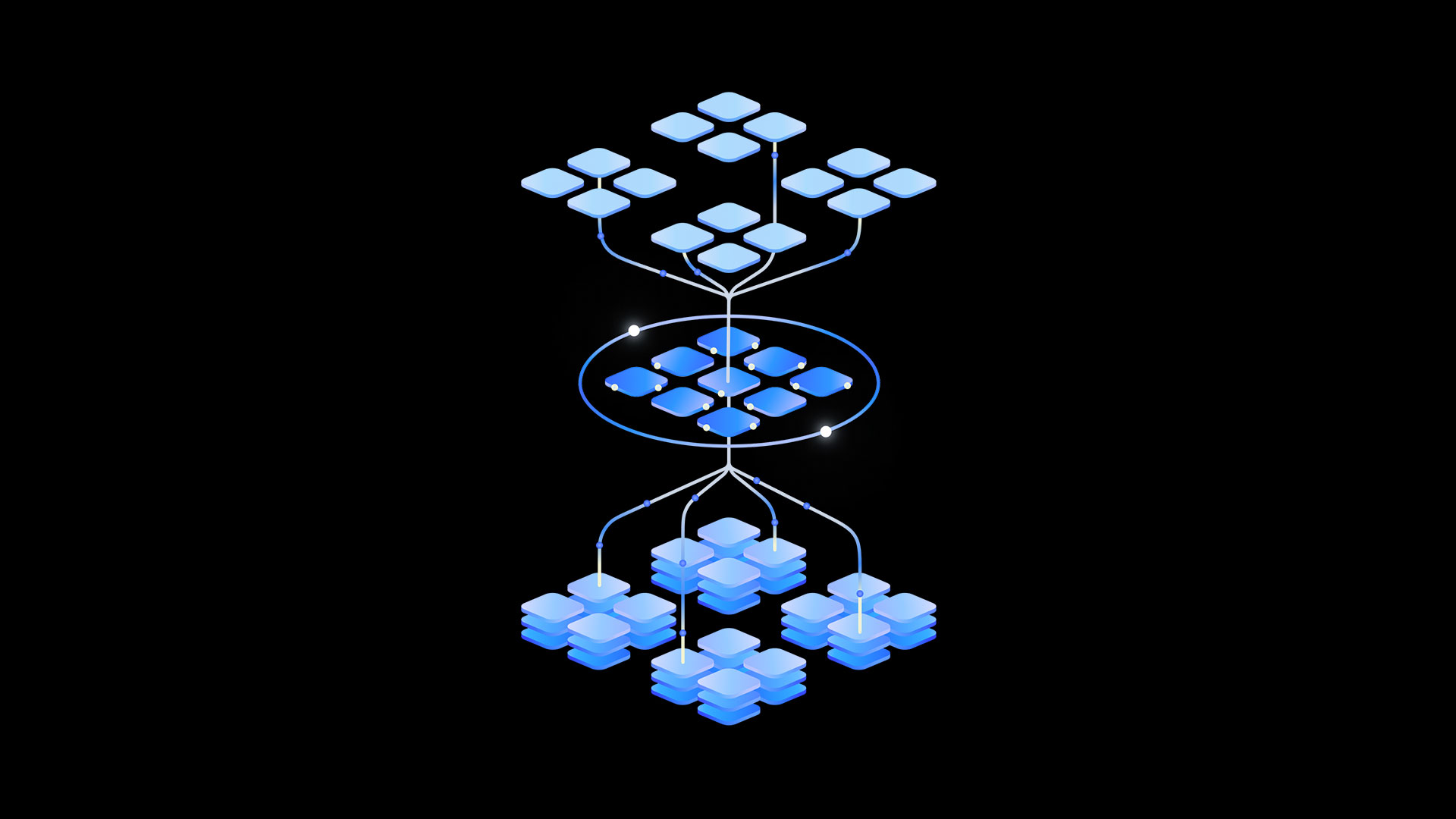
Fundamentally, it relies on a botnet of compromised devices spread across the internet, enabling malicious actors to cycle through numerous IP addresses in a short span of time. Two primary variants of fast flux have been identified:
In single flux attacks, a single domain is linked to dozens of rotating IP addresses, often hosted on compromised devices within botnets. For example, a domain like malwaredomain[.]com might resolve to IP addresses in Germany, Brazil, and Japan within minutes, forcing defenders to chase ephemeral endpoints.

Double flux adds another layer of obfuscation by dynamically rotating not just IP addresses but also the DNS name servers responsible for resolving the domain.
This creates a recursive loop of shifting infrastructure, making takedown efforts nearly impossible. Security analysts at Silent Push observed the Russian state-linked group Gamaredon using double flux to maintain C2 channels, cycling through over 100 IP addresses daily across autonomous systems in Europe and Asia.

While fast flux can have legitimate uses in content delivery networks (CDNs) or load balancers, its exploitation by cybercriminals poses significant risks.
How Threat Actors Use Fast Flux
The technique’s resilience and anonymity have made it a staple in high-stakes cyber operations, reads the CISA report.
Phishing and Fraud: Fast flux enables threat actors to rapidly deploy and dismantle phishing sites. A 2024 campaign targeting Australian banks used 300+ transient domains to host credential-stealing pages, each active for less than an hour before DNS records shifted. offering customers a mechanism to redirect traffic to “dummy servers” while shielding legitimate malicious servers from detection.
Ransomware Campaigns: Hive and Nefilim ransomware groups employed fast flux to sustain operations during 2021–2023 attacks. By hosting encryption keys and exfiltration portals on fast flux networks, they evaded IP-blocking measures long enough to extort millions from victims.
Bulletproof Hosting (BPH) Services: Underground providers like the Russian-based “BreachForums” now advertise fast flux as a premium feature. One 2023 dark web post boasted automated “dummy server interfaces” to bypass Spamhaus blocklists, ensuring phishing pages and botnet managers remain online despite abuse reports.
Fast flux has emerged as a robust enabler of cybercrime. Key applications include:
- Command-and-Control (C2) Operations: Threat actors use fast flux to mask their C2 servers, ensuring uninterrupted coordination of malware or botnets.
- Phishing Campaigns: Phishing websites leveraging fast flux remain accessible even after earlier URL takedowns, helping actors harvest sensitive data or distribute malware.
- Illicit Marketplaces: Online forums, fake shops, and other criminal hubs use fast flux to avoid disruption by law enforcement.
Detection and Mitigation Challenges
Detecting fast flux activity is challenging due to its resemblance to legitimate behaviors in CDNs or dynamic hosting setups. Cybersecurity organizations recommend the following strategies to counteract fast flux threats:
- Anomaly Detection: Monitoring DNS query logs for unusual activity, such as frequent IP changes or low time-to-live (TTL) values.
- Threat Intelligence Integration: Leveraging reputation services and identifying domains associated with fast flux activity.
- Collaborative Defense: Sharing fast flux-related threat indicators (e.g., domains and IPs) with trusted cybersecurity communities.
Moreover, organizations can benefit from Protective DNS (PDNS) services and sinkholing techniques to disrupt fast flux infrastructure and analyze traffic patterns for compromised devices.
BPH providers have emerged as critical enablers, offering “fast flux-as-a-service” to lower barriers for entry. A 2025 ACSC report highlighted a Netherlands-based BPH firm providing clients with pre-configured flux networks, complete with geo-distributed domains and rotating ASNs.
Such services allow even novice attackers to launch resilient campaigns, as evidenced by the 2024 GammaDrop malware campaign, which leveraged Cloudflare tunnels and flux DNS to bypass traditional defenses.
Investigate Real-World Malicious Links & Phishing Attacks With Threat Intelligence Lookup - Try 50 Request for Free
The post Hackers Leveraging Fast Flux Technique to Evade Detection & Hide Malicious Servers appeared first on Cyber Security News.



































































![Rapidus in Talks With Apple as It Accelerates Toward 2nm Chip Production [Report]](https://www.iclarified.com/images/news/96937/96937/96937-640.jpg)








































































































.webp?#)
_Christophe_Coat_Alamy.jpg?#)









































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)




















































































![From drop-out to software architect with Jason Lengstorf [Podcast #167]](https://cdn.hashnode.com/res/hashnode/image/upload/v1743796461357/f3d19cd7-e6f5-4d7c-8bfc-eb974bc8da68.png?#)







































































-Nintendo-Switch-2-–-Overview-trailer-00-00-10.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)


























































.webp?#)