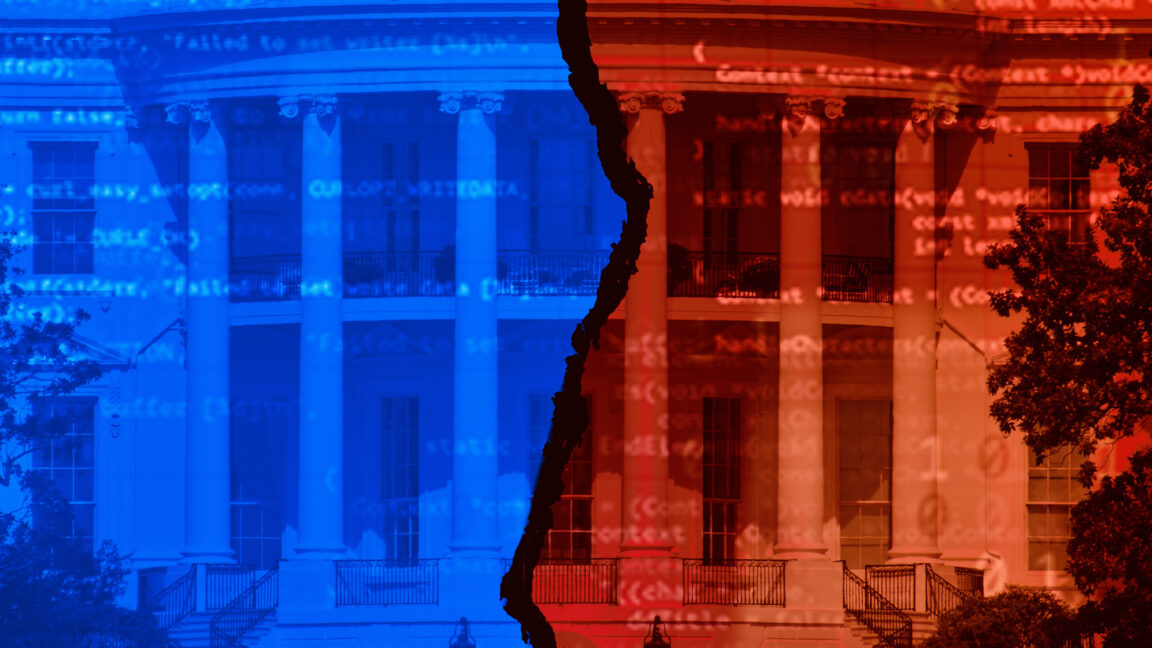
Ivanti products targeted by dangerous malware yet again
A patch, a reboot, and a few more steps, should do the trick.

- CISA is warning of new malware targeting vulnerable Ivanti products
- Multiple products, vulnerable to a 2024 flaw, are being targeted
- The malware can create web shells, harvest credentials, and more
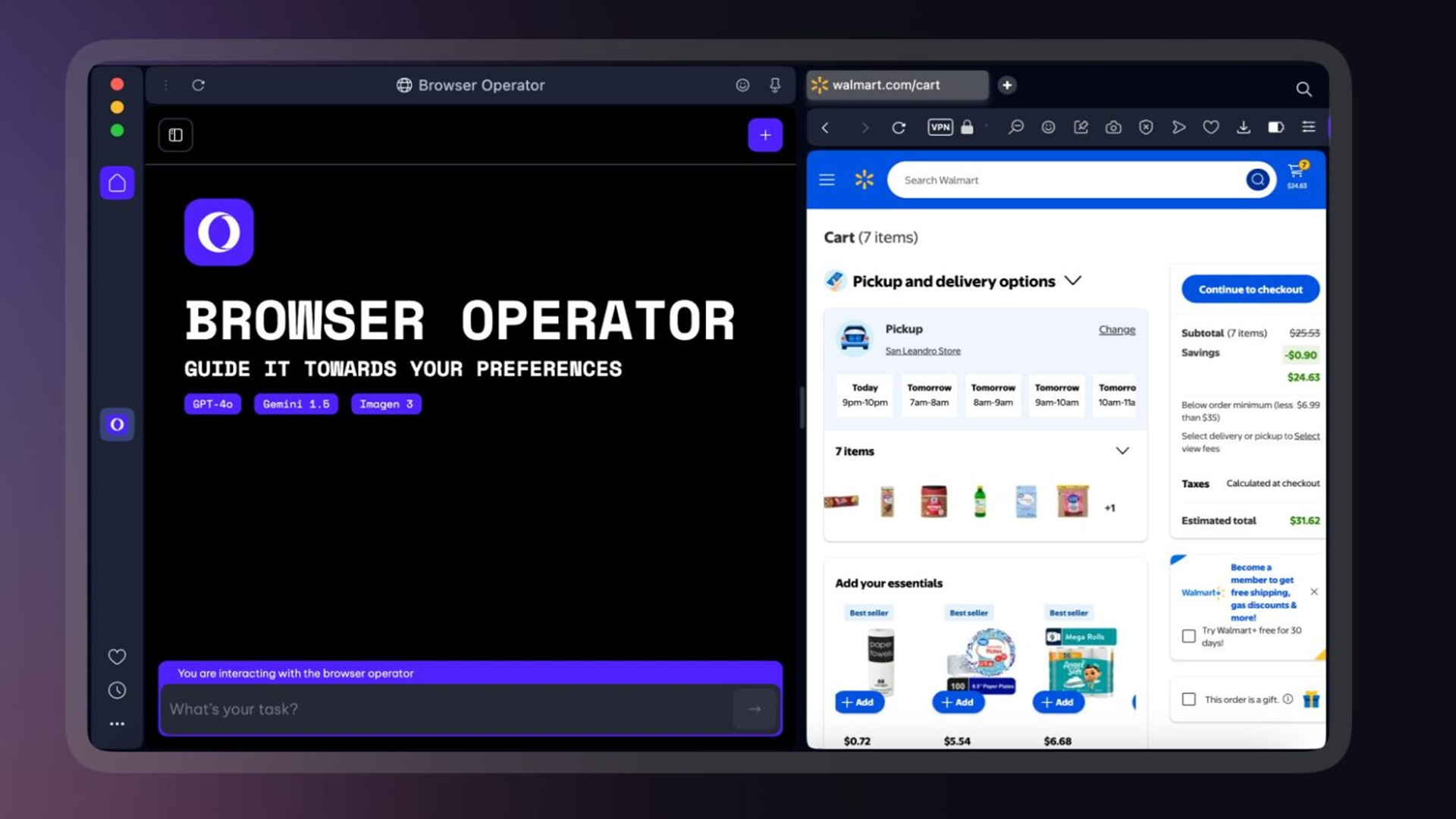
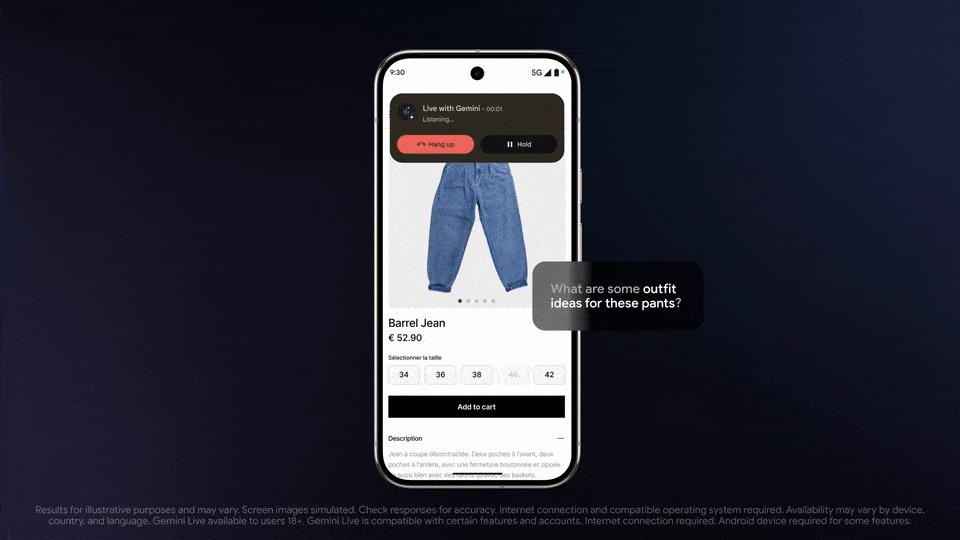
Multiple Ivanti products are being targeted by a piece of malware called RESURGE, a new security advisory published by the US Cybersecurity and Infrastructure Security Agency (CISA) has said, detailing both the malware and the vulnerability being exploited to deploy it.
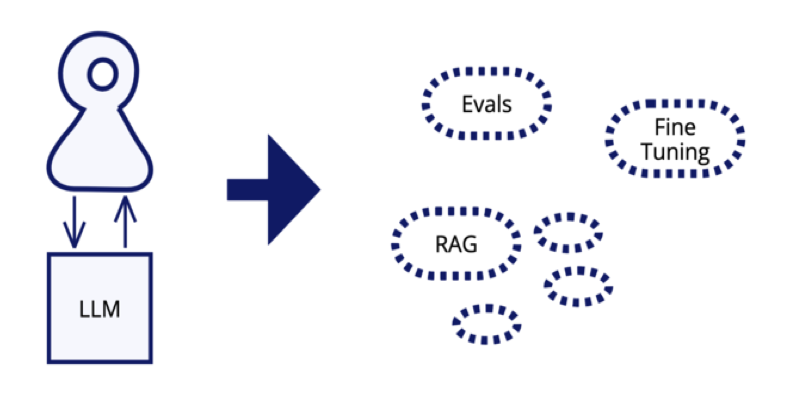
Resurge is a variant of SPAWNCHIMERA, a piece of malware targeting Ivanti Connect Secure appliances, enabling unauthorized access and persistent control over vulnerable endpoints.
While RESURGE can also survive reboots, the malware can also create web shells, manipulate integrity checks, modify files, and use the web shells to harvest credentials, create accounts, reset passwords, and escalate permissions.

Monitor your credit score with TransUnion starting at $29.95/month
TransUnion is a credit monitoring service that helps you stay on top of your financial health. With real-time alerts, credit score tracking, and identity theft protection, it ensures you never miss important changes. You'll benefit from a customizable online interface with clear insights into your credit profile. Businesses also benefit from TransUnion’s advanced risk assessment tools.
Preferred partner (What does this mean?)View Deal
Remote code execution risks
Furthermore, RESURGE can copy the web shell to the Ivanti running boot disk and manipulate the running coreboot image.
To infect the devices with RESURGE, threat actors are abusing CVE-2025-0282, a critical stack-based buffer overflow vulnerability in Ivanti Connect Secure, Policy Secure, and Neurons for ZTA gateways. It allows remote unauthenticated attackers to execute arbitrary code, and has been exploited in the wild since mid-December 2024.
CISA added the threat to its KEV catalog in early January 2025, noting the vulnerable software includes Ivanti Connect Secure (before version 22.7R2.5), Ivanti Policy Secure (before version 22.7R1.2), and Ivanti Neurons for ZTA gateways (before version 22.7R2.3).
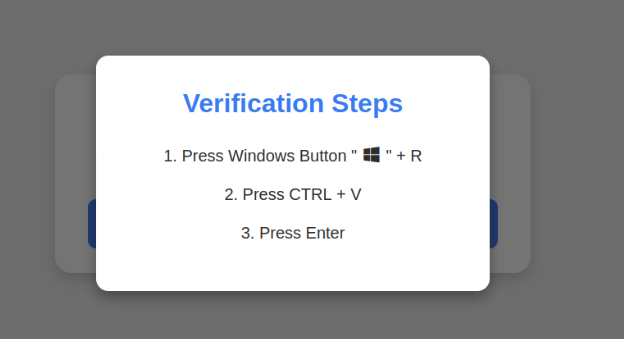
There are a number of things companies could do to mitigate the risk, CISA says.
“For the highest level of confidence, conduct a factory reset,” the advisory says. “For Cloud and Virtual systems, conduct a factory reset using an external known clean image of the device.”
Furthermore, users should reset credentials of privileged and non-privileged accounts, reset passwords for all domain users and all local accounts, review access policies to temporarily revoke privileges/access for affected devices, reset the relevant account credentials or access keys, and monitor related accounts, especially administrative accounts.
Via The Register
You might also like
- Ivanti warns another critical security flaw is being attacked
- We've rounded up the best password managers
- Take a look at our guide to the best authenticator app

































































![Apple Releases iOS 18.5 Beta and iPadOS 18.5 Beta [Download]](https://www.iclarified.com/images/news/96907/96907/96907-640.jpg)
![Apple Seeds watchOS 11.5 to Developers [Download]](https://www.iclarified.com/images/news/96909/96909/96909-640.jpg)
![Apple Seeds visionOS 2.5 Beta to Developers [Download]](https://www.iclarified.com/images/news/96911/96911/96911-640.jpg)
![Apple Seeds tvOS 18.5 Beta to Developers [Download]](https://www.iclarified.com/images/news/96913/96913/96913-640.jpg)







































































































































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)


































































































![Is this a suitable approach to architect a flutter app? [closed]](https://i.sstatic.net/4hMHGb1L.png)