Watch out! Don’t fall victim to these fake CAPTCHA scams on the web
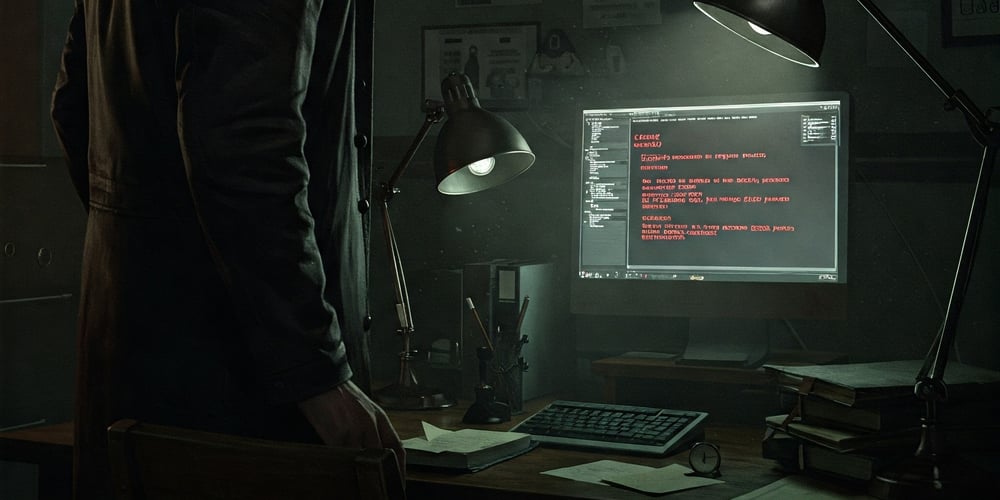
You’re likely well-acquainted with classic CAPTCHA tests on websites. You know, the thing where you have to click to confirm you aren’t a robot? Type in the strange-looking letters and numbers? Select all the traffic lights, the buses, the motorcycles, that sort of thing? These tests are mostly nuisances and data collection traps, but hackers are now leaning into CAPTCHAs as a way to trick users into installing malware. At least, that’s what security experts are increasingly warning about. Last month, MalwareBytes Labs spotted one such fake CAPTCHA that had you paste some “verification” text into the Windows Run prompt. Recently, there have also been reports of a malware called “Quakbot” that uses an even more dangerous variant of the CAPTCHA scam. How do CAPTCHA scams work? Hack attacks via CAPTCHAs are dangerous because users click on them out of habit when they appear on websites. Hackers are now exploiting this instant-reaction behavior with fake pop-up messages that look strikingly similar to real CAPTCHA tests. Here, too, users are asked to click on a box to solve a test. However, when you click on that box, you end up redirected to other pages. Further actions ensure that dangerous commands are copied to your clipboard, making it possible for attackers to run those dangerous commands on your computer without authorization. In some cases, these CAPTCHAs even prompt you to press certain key combinations that directly invoke Windows PowerShell or execute certain commands on your device. That’s why you should be extra suspicious of any CAPTCHA request that asks you to do anything unusual. These types of attacks are called ClickFix CAPTCHA attacks because they use social engineering to trick you into clicking fake CAPTCHAs and other elements, which then trigger malicious responses. These attacks are surprisingly effective To keep you off your toes, every subsequent click in a ClickFix CAPTCHA attack is disguised with additional “verification requests” that hide the malicious nature of what you’re doing. In the worst case, it ends with you unknowingly executing a malware script that takes over your PC. CAPTCHA attacks reportedly have a higher success rate than other scam attempts because of their novel psychological tricks that prey on reflexive behavior when our guards are down. The only real protection is to remain vigilant, especially when visiting unfamiliar websites. And, of course, having reliable antivirus software that protects against threats.

You’re likely well-acquainted with classic CAPTCHA tests on websites. You know, the thing where you have to click to confirm you aren’t a robot? Type in the strange-looking letters and numbers? Select all the traffic lights, the buses, the motorcycles, that sort of thing? These tests are mostly nuisances and data collection traps, but hackers are now leaning into CAPTCHAs as a way to trick users into installing malware.
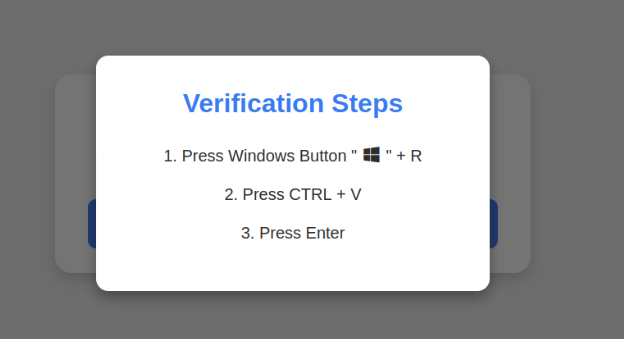
At least, that’s what security experts are increasingly warning about. Last month, MalwareBytes Labs spotted one such fake CAPTCHA that had you paste some “verification” text into the Windows Run prompt. Recently, there have also been reports of a malware called “Quakbot” that uses an even more dangerous variant of the CAPTCHA scam.
How do CAPTCHA scams work?
Hack attacks via CAPTCHAs are dangerous because users click on them out of habit when they appear on websites. Hackers are now exploiting this instant-reaction behavior with fake pop-up messages that look strikingly similar to real CAPTCHA tests.
Here, too, users are asked to click on a box to solve a test. However, when you click on that box, you end up redirected to other pages. Further actions ensure that dangerous commands are copied to your clipboard, making it possible for attackers to run those dangerous commands on your computer without authorization.
In some cases, these CAPTCHAs even prompt you to press certain key combinations that directly invoke Windows PowerShell or execute certain commands on your device. That’s why you should be extra suspicious of any CAPTCHA request that asks you to do anything unusual.
These types of attacks are called ClickFix CAPTCHA attacks because they use social engineering to trick you into clicking fake CAPTCHAs and other elements, which then trigger malicious responses.
These attacks are surprisingly effective
To keep you off your toes, every subsequent click in a ClickFix CAPTCHA attack is disguised with additional “verification requests” that hide the malicious nature of what you’re doing. In the worst case, it ends with you unknowingly executing a malware script that takes over your PC.
CAPTCHA attacks reportedly have a higher success rate than other scam attempts because of their novel psychological tricks that prey on reflexive behavior when our guards are down. The only real protection is to remain vigilant, especially when visiting unfamiliar websites. And, of course, having reliable antivirus software that protects against threats.






























































![Apple Releases macOS Sequoia 15.5 Beta to Developers [Download]](https://www.iclarified.com/images/news/96915/96915/96915-640.jpg)
![Amazon Makes Last-Minute Bid for TikTok [Report]](https://www.iclarified.com/images/news/96917/96917/96917-640.jpg)
![Apple Releases iOS 18.5 Beta and iPadOS 18.5 Beta [Download]](https://www.iclarified.com/images/news/96907/96907/96907-640.jpg)



































































































.jpg?#)








































































![[The AI Show Episode 142]: ChatGPT’s New Image Generator, Studio Ghibli Craze and Backlash, Gemini 2.5, OpenAI Academy, 4o Updates, Vibe Marketing & xAI Acquires X](https://www.marketingaiinstitute.com/hubfs/ep%20142%20cover.png)


































































































![Is this a suitable approach to architect a flutter app? [closed]](https://i.sstatic.net/4hMHGb1L.png)




















![[DEALS] Microsoft Office Professional 2021 for Windows: Lifetime License (75% off) & Other Deals Up To 98% Off – Offers End Soon!](https://www.javacodegeeks.com/wp-content/uploads/2012/12/jcg-logo.jpg)

























-Nintendo-Switch-2-–-Overview-trailer-00-00-32-(1)_HCqcxO1.png?width=1920&height=1920&fit=bounds&quality=80&format=jpg&auto=webp#)